Partnering with a third-party cybersecurity firm like Pattern Drive Private Limited would prove to be the most cost-effective solution.

The rise in data breaches and cyber-attacks now costs the public sectors and businesses millions per year, while cybersecurity is relatively higher on the strategic plan.
The business leaders occupying both operational and strategic roles must answer some vital questions:
By collectively aligning the cybersecurity assessments, your organization can receive the right strategy as well as the transformation program for protecting the assets and sensitive data.
Our cybersecurity consulting services provide you with insight into your company’s security management bearing assessments of your sensitive data, applications, and critical infrastructures. We work hand in hand with you for defining and implementing the correct strategy and target operating model.
We ensure your operations support, security design, business continuity and strategic objectives. With the help of proper cybersecurity strategic planning of the future as a part of the digital transformation journey, you will be more confident about staying compliant and achieving cost savings. Our consulting guidelines are stressed upon a very rational framework that includes human factor, market standards and economics.
There are three common reasons why businesses choose us for their help.

Our cybersecurity engineers literally have no political profit for achieving within the business of a client. Additionally, there are no interests to be worried about when it comes to offering solutions and recommendations.

It would probably be much more cost-effective for our clients to bring us into their work culture if we lacked skill level, experience and expertise. However, our cybersecurity engineers possess the complete and immediate reach-back to all of Pattern Drive. This offers multiple technical capabilities, experiences and certifications for every engagement.
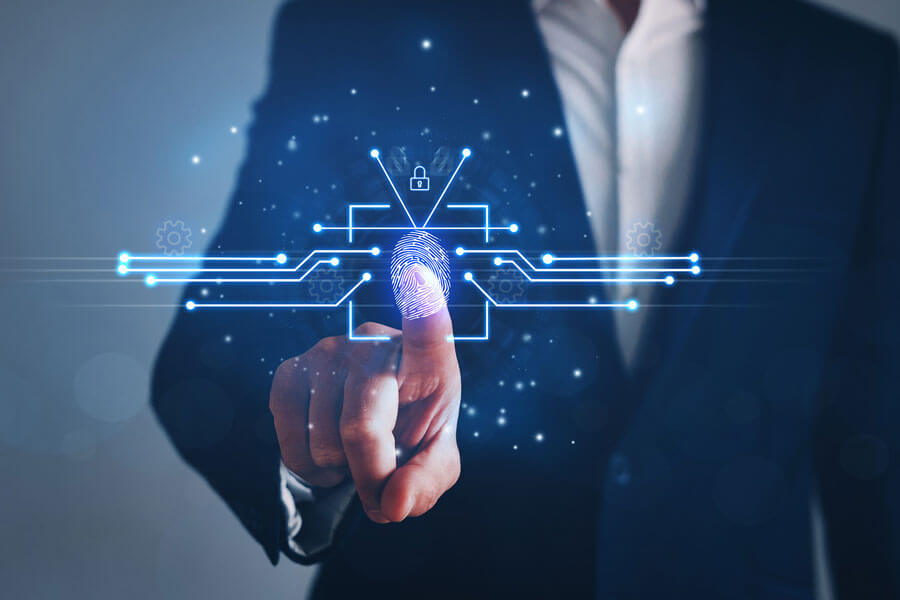
A company’s information security policies and procedures establish the protocol to implement the security measures for protecting its data assets. Each firm requires to be aware of the data sensitivity and its responsibilities to protect it. Nevertheless, compelling information security policies and procedures fix the unified organisation's security tone and conduct personal awareness of their expectations.