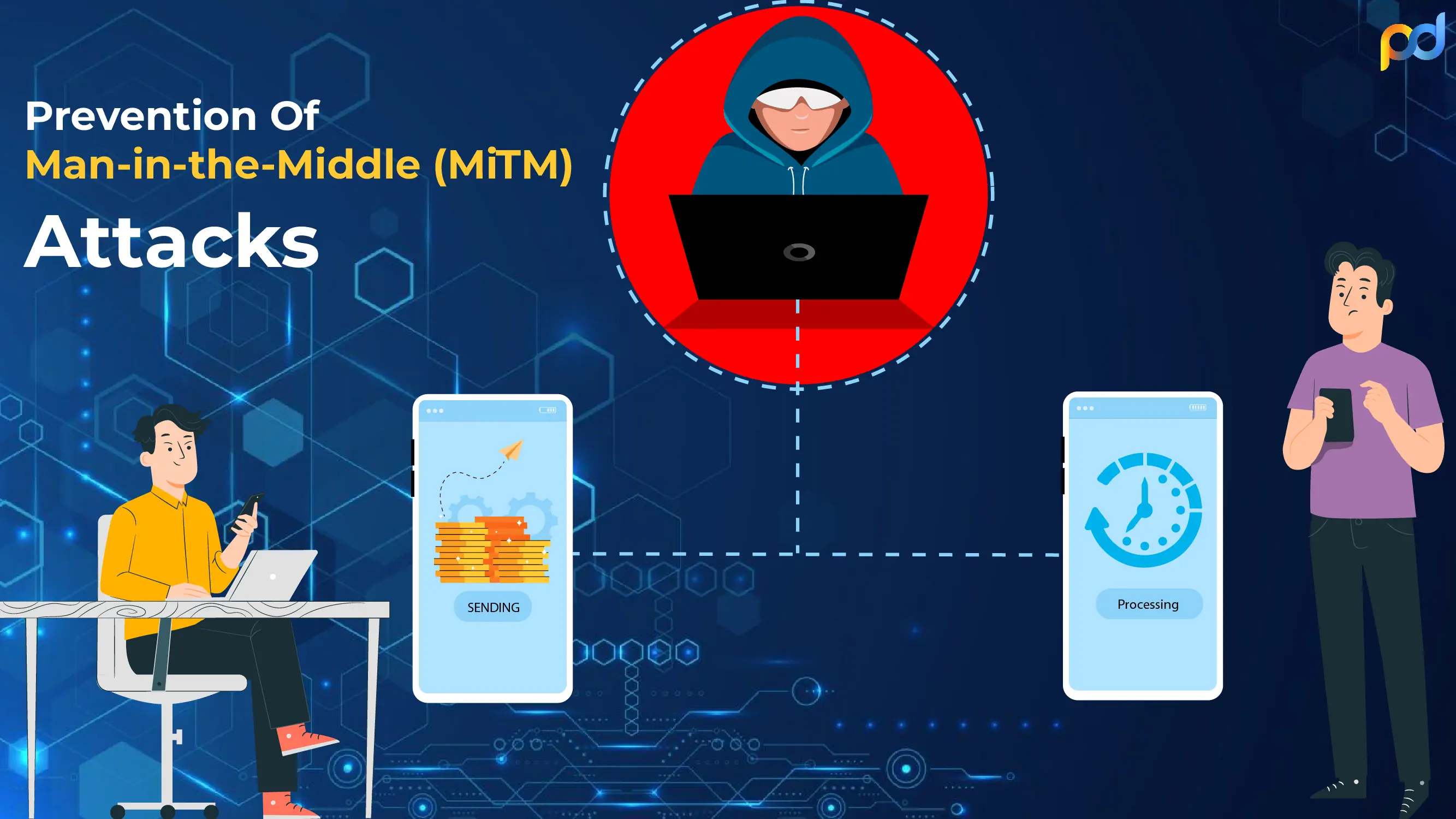
How To Prevent Risky Man-in-the-Middle Attack (MiTM) Types?
02-12-2022 | Alex Smith
Modern businesses run with the help of data and sending confidential information is an essential part of these contemporary businesses. This includes sending important emails, retrieving data from int...
Read More